Like most people who want to sign up for a VPN, you’ve probably heard the word “protocol” but never took the time to learn more about it.
VPN Protocols Explained
A VPN protocol is one of the most important parts of a VPN service that can help determine the quality of encryption and security. Whether you’re using a VPN to change your IP address or to change where you stream from, it helps to know what’s going on behind the scenes.
Read on to learn about the different types of VPN protocols and what we suggest if you want a good balance of security and privacy without sacrificing speed and ease of use.
What is a VPN Protocol
A VPN protects your data through encryption and hiding your IP address so you can access the geo-restricted content on websites and streaming services. So that no one, not even your internet service provider (ISP), can use your information. This process is done to secure the data within the user and the VPN server tunnel. In other words, whenever you join a VPN server, your connection requests are encrypted before being sent to the server. Once the data has been communicated to the right person, it is changed back into a format that can be read.
Remember that hackers can still do bad things even if you use VPN encryption. Instead, it changes your data into a file that can’t be read, so it can’t be read. With a VPN protocol, the software follows a set of codes that control how your connection works.
Most VPN companies will also connect users to the protocol that works best with the network they are on. But if you want to set up your VPN protocol, you can do so based on your VPN service provider.
The Different Types of VPN Protocols
VPN protocols are different for each VPN service. Here are some of the most typical types:
1. SSTP

Secure Socket Tunneling Protocol (SSTP) is a Microsoft-only standard, so setting it up on a Windows-based device is easy but can be difficult on Linux and macOS.
SSTP supports the AES-256 encryption standard. This is a symmetric key cipher that can be used by both the sender and user of data packets. Compared to the 128-bit and 192-bit forms, it is the most secure regarding key length size, making it impossible to crack using brute force.
Another advantage of SSTP is that it can easily get around firewalls to ensure a connection using TCP port 443 is smooth. However, due to Microsoft’s affiliation with the NSA, it is rumored to be a little less secure than L2TP/IPSec. Because of this, many VPN services warn against using it. Lastly, because it uses SSL 3.0 encryption, it can only partially inspected, and the encryption process may slow down the speed.
2. PPTP

Point-to-Point Tunneling Protocol (PPTP) was first used for dial-up data in 1999 when Windows 95 was still a popular operating system. Since then, it has become most people’s normal VPN protocol. This protocol is already built into many platforms, including Windows, macOS, Android, and iOS, and is the fastest compared to other protocols. These days, it’s rare to find a device that doesn’t handle PPTP.
However, the lack of security brought on by the very low 128-bit encryption standard negates the speed advantage set. Due to the lack of privacy and security when PPTP sends data packets, many VPN service companies have switched to better protocols. Because of this, it is easy to figure out what it says.
It also uses the TCP 1723 port and IP protocol 47 Generic Routing Encapsulation (GRE) to let PPTP tunneled information pass through the router. If you’re using this protocol in a place that doesn’t allow VPN connections, blocking it with a firewall is easy.
If you only want to stream content blocked in your country, then a PPTP protocol will do. But don’t use this to keep your privacy and security.
3. L2TP/IPSec

Layer 2 Tunneling Protocol (L2TP) does not have its encryption feature. Instead, it rests on internet protocol security (IPSec), which is used to authenticate and encrypt data packets. It is also easy to set up, even though L2TP/IPSec is already on most computers.
But it’s usually slow because it has to encapsulate data twice, compared to other protocols that only do it once.
Some cybersecurity agencies, like the U.S. National Security Agency (NSA), are rumored to have broken the protocol. Lastly, since it uses UDP port 500, it is easy to block using a firewall. So, there are better choices than the PPTP option.
4. IKEv2

One of the newest VPN protocols is Internet Key Exchange version 2 (IKEv2). Microsoft and Cisco made it. It uses IPSec encryption and is mostly available on Windows, iOS, and other platforms. You may need a different version if you use a different working system.
When a user switches from mobile to home WiFi using the Mobility and Multihoming protocol, one of the protocol’s benefits is its quick connection recovery when the internet connection drops unexpectedly. So, the best mobile devices for this protocol use 3G or 4G LTE.
Security isn’t an issue either since many tech reviews have said that encryption works well.
5. WireGuard
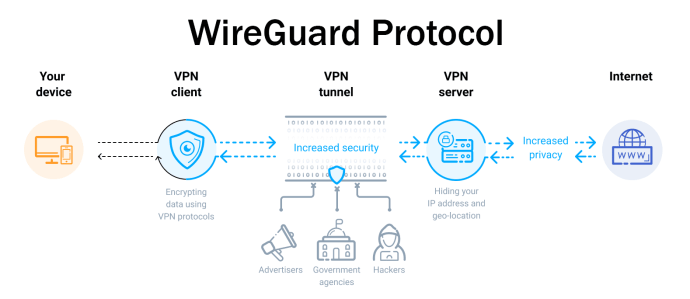
This is a new protocol that also uses the best cryptographic technology to make security better. Like OpenVPN, it is free and open-source, making auditing and debugging easy.
The codebase only has 4,000 lines, making it one of the simplest and lightest choices. On the other hand, OpenVPN has nearly 400,000 lines of code. Speed is also not an issue since tests have shown that it is faster than the IPSec protocol.
Lastly, instead of using the AES-256 encryption standard, its key routing protocols use Curve25519, SipHash24, ChaCha20, BLAKE2s, and HKDF, among others, making it one of the most secure VPN protocols available today.
Although many VPN service providers have already assured that they have a no-logs policy even with such an issue, some security experts have noticed that WireGuard always assigns the same IP address each time a user connects to a VPN service.
6. OpenVPN

This protocol uses the OpenSSL library so users are required to use a third-party software. It is a common default protocol used by VPN service providers. You may also verify if your VPN service provider has a setup requirement for this.
Its AES-256 encryption specification is also regarded as its main advantage. And since it’s an open-source protocol, auditing the code is easy. Like SSTP, it uses TCP port 443 to make it much harder to block when going through firewalls.
However, the speed that OpenVPN has is not the fastest available, although it isn’t slow either. In addition, it is difficult to set up unless the user is knowledgeable on using such a solution.
7. Lightway

This new VPN protocol, developed by ExpressVPN and based on WireGuard, was inspired. Lightway has fewer lines of code, about 2,000 lines, so it’s faster and uses less power on your device. And when there is less code, users can quickly audit it to find and fix any flaws they may find.
Secure Socket Layer/Transport Layer Security (SSL/TLS) protocols are also supported by a cryptography tool called WolfSSL, which is easy to set up and use. To ensure integrity, message privacy, and improved authentication, the NSA uses these to better protect its online interactions from unauthorized access and tampering. Lightway’s security potential has also been tested and confirmed by a separate security body.
If you’re using a mobile device and want faster loading without draining your battery, choose ChaCha20, a much faster cipher than AES-128 GSM.
Last but not least, Lightway has the fastest speeds. If your connection suddenly drops, it instantly reconnects you. With other VPN protocols, this process can take at least 15 seconds. Our independent tests also showed that it is about 2 Mbps faster than WireGuard and other protocols when downloading and about 3 Mbps faster when uploading.
Comparing Different VPN Protocols
[table]
| PPTP | L2TP/IPSec | SSTP | IKEv2 | OpenVPN | WireGuard | Lightway | |
| Platform | Windows, macOS, iOS, Android |
Windows, macOS, iOS, Android |
Windows | Windows, iOS |
Windows, macOS, iOS, Android |
Windows, macOS, iOS, Android |
Windows, macOS, iOS, Android |
| Speed | Very Fast | Slower | Moderate | Fast | Fast | Very Fast | Very Fast |
| Encryption | Basic encryption | IPSec | SSL 3.0 | IPSec | AES | Curve25519, SipHash24, ChaCha20, BLAKE2s, and HKDF | AES |
| Security | Weak | Good | Good | Good | Secured | Secured | Top-notch wolfSSL |
| Firewall | Can be blocked | Can be blocked | Difficult to be blocked | NA | Difficult to be blocked | Difficult to be blocked | Difficult to be blocked |
| P2P | Acceptable | Acceptable | Good | Good | Good | Good | Good |
Which VPN Protocol is the Best
Based on the comparisons above, it’s clear that the Lightway protocol is the best VPN protocol. It uses advanced technology to let you connect quickly when switching servers or restoring your connection. Because it only has the features that a consumer VPN should have, making every online experience efficient and secure, it also drains your battery much less than other protocols compared to other protocols.
In addition to Lightway, ExpressVPN lets users choose from IKEv2 and OpenVPN.
Frequently Asked Questions
Why is a VPN protocol important when selecting a VPN service?
Your connection to a network is encrypted using secure encryption techniques under the control of a VPN protocol. It also helps you determine how much your speed will change when using a VPN.
Do all VPN services provide the same level of encryption?
No. Many VPN service providers say they have the best encryption technology but need help even to use pre-shared keys (PSKs) to make a more complicated encryption key that can withstand brute-force attacks.
Why does my connection speed drop when I use VPN?
Aside from the quality of your Internet connection and how far you are from the server you want to use, encrypting your connection will take time and more power. This means that you must give up some speed whenever you want more security by using a more reliable VPN protocol.
What should I look for in a VPN service?
Research the VPN protocol, speed, security, privacy, and customer service. The more secure your online browsing will be, the better encryption it gives you. Today, the Lightway VPN protocol that ExpressVPN uses is considered one of the best. This is because it ensures you can quickly pick up your connection when you switch networks or lose it.
Which VPN protocol is best for gaming?
Lightway is a great choice for gaming because it is very stable and has fast speeds.